CBSE Class 12 Informatics Practices Notes Chapter 1 Computer Networking Pdf free download is part of Class 12 Informatics Practices Notes for Quick Revision. Here we have given NCERT Class 12 Informatics Practices Notes Chapter 1 Computer Networking.
CBSE Class 12 Informatics Practices Notes Chapter 1 Computer Networking
Applications of Network
Some of the applications of network are discussed below:
- Sharing of Information In a network, the users can share information, data and text easily to other users. Different users can share the same database, having different levels of access control.
- Sharing of Peripherals The computers, in a network, can share common peripherals, e.g. one highly speed common printer can be used for all computers in a network.
- Communication In a network environment, communication between different users or computers is possible. By which we can send messages, documents (text), data files, graphics, videos, images or an e-mail to different users over the network.
- Accessing Remote Database We can access the remote database and retrieve information according to our requirement in a network. We can booked tickets for airlines and trains or even we can book a room in a hotel at any destination by a network.
Communication Media
Communication media of a network refer to the connecting media, through which different computers in a network are interconnected together. The communication media can also be referred as communication channels. The communication media can be grouped into two categories:
Wired Technologies (Guided Media)
When the computers in a network are interconnected through a wire or cable, then such a medium is categorised under wired technologies. Among wired technologies, ethernet cable, co-axial cable, optical fiber, etc., are included.
1. Ethernet Cable It is also known as twisted pair cable. There are two identical wires wrapped together and twisted around each other.
Advantages of Ethernet Cable
- It is simple and physically flexible.
- It is inexpensive and easy to install and maintain.
Disadvantages of Ethernet Cable
- Using ethernet cable, signals cannot be transported over long distances without using repeaters.
- It is not suitable for broadband applications as it has low bandwidth capabilities.
2. Co-axial Cable It consists of a solid core wire surrounded by foil shield, each separated by some insulator. The inner solid core wire carries the signal through the network and the shield is used to provide earthing or ground. Co-axial cable is commonly used in transporting multi-channel television signals in cities.
Advantages of Co-axial Cable
- The data transmission quality in co-axial cable is better than twisted pair cable, yet it is affordable.
- Co-axial cables can be used successfully in shared cable network.
- It can be used effectively for broadband transmission.
Disadvantages of Co-axial Cable
- Co-axial cable is more costly than twisted pair cable.
- The co-axial cable is not compatible with twisted pair cable. So, both of these cables cannot be used together in a network.
3. Optical Fiber It consists of thin strands of extruded glass silica or plastic, slightly thicker than human hair, which are capable of carrying light signals from a source at one end to another end. At the source, there is a Light Emitting Diode (LED) or a Laser Diode, which modulates the data into light beam using frequency modulation techniques. At the receiving end, the data are demodulated into computer readable form.
An optical fiber cable contains following three parts:
- Core It is the innermost part, which is made up of glass or plastic through which the light signals travels.
- Cladding The cladding covers the core and reflects the light beam back into the core.
- Protective Coating The protective coating is outside the cladding for the protection of the optical fiber.
Advantages of Optical Fiber
- It is immune to electrical and magnetic interference i.e. noise in any form cannot harm the data because, the information is travelling on a modulated light beam.
- It is highly suitable for rigid industrial environments.
- Optical fiber cables can be used for broadband transmission, where several channels (i.e. frequency bands of) are handled in parallel and there is possibility of mixing up of data transmission channels with other channels.
Disadvantages of Optical Fiber
- Connecting either two fibers together or a light source to a fiber is a difficult process.
- Because of noise immunity, optical fibers are virtually impossible to tap. In order to intercept the signal, the fiber must be cut and a detector must be inserted which is not possible.
- Optical fiber cables are more difficult to solding (joint of one or more cable).
Wireless Technologies (Unguided Media)
When the computers in a network are interconnected and transmitted through waves, which are travelled through air, water or vacuum, then such a medium is categorised under wireless technologies. Among wireless technologies are bluetooth, infrared, microwave, radio link, satellite, etc., are included.
1. Bluetooth It is a wireless technology, which is used for exchanging data over short distances from fixed and mobile devices. Such types of networks are categorised under personal area network. Bluetooth was developed by telecom vendor Ericsson in 1994. Today, bluetooth is managed by the Bluetooth Special Interest Group, which has more than 14000 member companies in areas of computing, telecommunication, electronics and networking. This occurs mostly on your cell phone but also occurs in other technology such as music players.
Advantages of Bluetooth
- It allows you to stay cord or cable free. So, you do not have to worry about finding the correct place to connect that extra long cord.
- Even though you are able to exchange data across your cell phones, you still have the ability to keep your information private.
- As it is already, but most likely it will be more dominant. You can use bluetooth on laptops, cell phones, music players, headsets, printers and many more other products.
Disadvantages of Bluetooth
- You are using up more battery power, when you leave your bluetooth enabled on your phone all day.
- Throughout all devices, when using bluetooth Internet, the connection can sometimes run very slow, so bluetooth Internet is not highly suggested for that cases
2. Infrared In this type of transmission, infrared light signals are used. Infrared signal are used in TV remotes, infrared wireless speakers, etc., as a mode of transmission.
In infrared transmission, signals are transmitted through the air but these signals cannot penetrate the walls.
Advantages of Infrared
- Low power requirements therefore ideal for laptops, telephones, personal digital assistants.
- Low circuitry costs $2-$5 for the entire coding/decoding circuitry.
- Simple circuitry no special or proprietary hardware is required, can be incorporated into the integrated circuit of a product.
Disadvantages of Infrared
- Blocked by common materials: people, walls, plants, etc., can block transmission.
- Line of sight: transmitters and receivers must be almost directly aligned (i.e. able to see each other) to communicate.
- Short range: performance drops off with longer distances.
3. Microwave In this type of transmission, signals are transmitted in the same way as the radio and television transmission. The requirement for microwave transmission is transmitter, receiver and the atmosphere. Under this mode of transmission parabolic antennas are mounted on the towers. These antennas send the signals in the atmospheric air. These signals are received by the receiver.
Advantages of Microwave
- Using microwave, signals can be transmitted in the air without using cables.
- Using microwave, communication is possible even in difficult terrain or over oceans.
Disadvantages of Microwave
- It is not a secured mode of communication.
- Microwave communication is affected by weather conditions such as rain, thunderstorms, etc.
4. Radio Link When two terminals are connected by using radio frequencies, then such type of communication is referred as radiowave transmission or radio link. Any radio transmission set-up has two parts viz., the transmitter and the receiver. Both the transmitter and the receiver use antennas to send and receive the radio signals.
Advantages of Radio Link
- It is a cheaper means of transmission than wired communication.
- It provides mobility and makes communication easy over difficult terrain.
Disadvantages of Radio Link
- It is not a secured mode of transmission.
- These signals are affected by the weather conditions like rain, thunderstorms, etc.
5. Satellite In this type of communication, data are transmitted through satellite. Under this arrangement, there is an earth station and a satellite placed in the stationary orbit, which is about 22300 miles above the earth’s surface. In satellite communication, the earth station transmits data towards the satellite and the satellite accepts these signals, amplifies them and then retransmits them towards the earth. These signals are captured by the receiver.
Advantages of Satellite
- In satellite communication, large area could be covered.
- This mode of transmission is very useful in multimedia transmission.
Disadvantages of Satellite
- Satellite communication is very costly. So, it is not suitable for personal or low budget communication.
- There is atmospheric loss of transmitted signals.
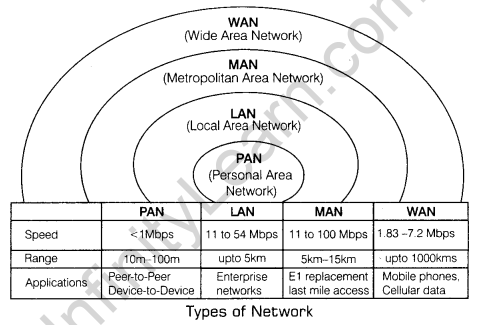
Types of Network
On the basis of coverage or geographical spread, a network can be divided into following types:
1. Local Area Network (LAN) When the network of computer is confined to a small or localised area such as school, office or building, it is known as Local Area Network (LAN). Computers or users in a local area network can share data, information, software and common hardware devices such as printer, modem, hard disk, etc.
2. Metropolitan Area Network (MAN) A metropolitan area network is the network which is spread over a city. The functions of a MAN is similar to LAN. Like a LAN, computers in a MAN are also capable of sharing data, information, software and hardware. The difference is only on the basis of geographical area coverage.
3. Wide Area Network (WAN) The network of computers which is spread across the countries probably over the entire world is known as a Wide Area Network (WAN).
- A WAN can be a group of several LANs interconnected together.
- The largest WAN is the Internet.
- The functions of WAN are also similar to a LAN or MAN.
4. Personal Area Network (PAN) The PAN refers to a computer network, which is used for communication among computer devices spread over a few meters. PAN may be wired (i.e. with the use of computer buses such as USB) or wireless using wireless network technologies such as bluetooth, wireless USB, Z-wave and ZigBee. Bluetooth personal area network(PAN) is also called a piconet. It can be composed of upto eight devices in a master slave relationship. The first bluetooth device is master and other devices are acting as slaves. Normally, its range is upto 10 m.
Network Topologies
The network topology refers to the arrangement or pattern of computers (i.e. nodes or workstations), which are interconnected in a network.
Commonly used network topologies are as follows:
1. Bus Topology Bus topology is also referred as linear topology. Under this arrangement, all nodes in the network are connected by a single length of transmission medium, which is normally a co-axial cable. Both ends of the cable are terminated by terminators. Data transmission from any workstation can travel in both directions.
Advantages of Bus Topology
- In bus topology, all nodes are connected through a single length of cable, so very short cable length is used.
- Extension of network is very easy in bus topology. We can connect new nodes along its length.
Disadvantages of Bus Topology
- When there is any problem in data communication with any node, whole network stops functioning.
- In case of any fault in data transmission, fault isolation is very difficult. We have to check the entire network to find the fault.
2. Ring Toplogy In ring or circular topology, the nodes are connected in a circular way. In such arrangement, each node is connected to exactly with its two neighbouring nodes. In other words, when the last node in a bus network is connected with first node and the entire network becomes circular network is known as a network using ring topology.
Advantages of Ring Topology
- Short cable length is required for connecting the nodes together.
- The architecture of network is simple and easy to maintain.
Disadvantages of Ring Topology
- In ring topology, each node is connected in a circular way with its two neighbouring nodes, so when there is transmission problem anywhere in the network, entire network stops functioning.
- Fault diagnosis is very difficult in a network formed using ring topology.
3. Star Topology In star topology, there is a direct and dedicated connection of every . node of the network with the central node or server. In star topology, the server is directly connected with each and every node in the network via a hub.
Advantages of Star Topology
- The star topology is the most reliable as there is a direct connection of every node in the network with the central node or server.
- If there is any problem in connection with any node, other nodes in the network are not affected.
Disadvantages of Star Topology
- Since, every node is directly connected with the central node or the server, so a large quantity of the cable is required.
- There is dependency on the central node. If there are some problems with the central node, entire network stops functioning.
4. Mesh Topology A network set-up where each computer and network device is interconnected with one another to provide an alternative route in case of the host is down or busy.
Advantages of Mesh Topology
- Excellent for long distance networking.
- Communication is also possible through the alternate route, if one path is busy.
Disadvantages of Mesh Topology
- Long wire/cable length, hence increase in the cost of installation and maintenance
- There are high chances of redundancy in many of the network connections.
- Set-up and maintenance of this topology is very difficult. Even administration of the network is tough.
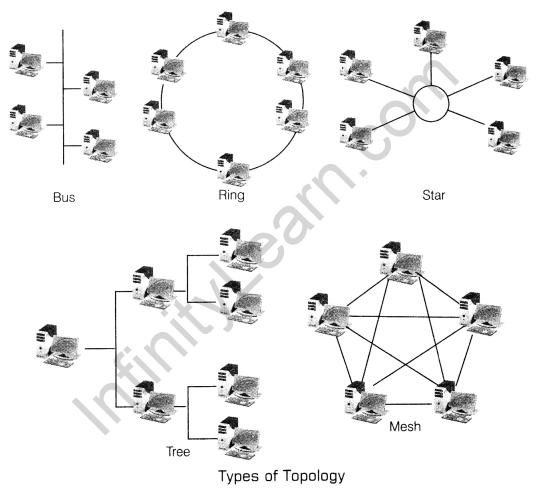
5. Tree Topology The tree topology is an extension and variation in bus topology. Here, the shape of a network is like an inverted tree, where the central node is at the root which is branching out as the network extends. Tree topology is suitable for the applications which have a hierarchical flow of data and control. Since, it is a modified form of bus topology, hence it is a hybrid topology.
Advantages of Tree Topology
- The tree topology simulates hierarchical flow of data. So, it is suitable for applications, where hierarchical flow of data and control is required.
- We can easily extend the network whenever required.
Disadvantages of Tree Topology
- There is a requirement of long cable length.
- In tree topology, there is dependency on the root node.
Network Devices
Network devices are the components used to connect computer and other electronic devices together, so that they can share files or resources like printers or fax machines. The most common type of network devices used by the public to set-up a Local Area Network (LAN) are hub, switch, repeater and if online access is desired, a high-speed modem.
1. Modem (Modulator/Demodulator) Modem is a device that converts digital signal to analog signal (modulator) at the sender’s site and converts back analog signal to digital signal (demodulator) at the receiver’s end, in order to make communication possible via telephone lines.
Functions of Modem The essential function of a modem is to create an easily transmitted and decode signal. Modem divides the information into packets called frames. They minimise the error that occur while the transmission of signals. Modems are of two types:
- Internal Modem It refers to the modem that is fixed within a computer, e.g. dial-up and wireless.
- External Modem A modem that resides in a self-contained box outside the computer system, e.g. USB modem, Cable modem.
2. Hub Hub is a device used to connect several computers together. It provides a centralised connection to several computers with the central node or server.
It is multi-slot device in which multi-port cards can be inserted to provide access to computers in the network.
Functions of a Hub A hub is a device that interconnects a number of computers or users. Whenever any data packet is received by any port in a workstation which may be an e-mail, graphics or any document, is forwarded to all remaining ports. Thus, the required data packet is transported to desired user or device.
There are two types of hub:
- Active Hub It amplifies the signals and passes from one connected device to another. These hubs are working as repeaters to boost up the signals.
- Passive Hub It simply passes signals from one connected device to another without making any changes.
3. Switch The switch is a hardware device used to divide or segment the network into smaller subnets or LAN segments. The main purpose of segmenting a large network into smaller segments is to prevent the traffic overloading in a network.
A switch forwards the data packet in a specific way over the network. It means the switch filters the data packet, when the same is passed to it and for the packet to the desired LAN segment.
Functions of a Switch
The switch is responsible for forwarding a data packet to a specific route or segment. For this purpose, the switch establishes a temporary connection between the source and the destination, when the data packet is transported the connection is terminated.
4. Repeater The repeater is a hardware device used in a network to amplify the weak signals, when they are transported over long distances. When the signal is transmitted over a line, then due to resistance and other causes it accumulates noise. Due to this noise, the quality of signal degrades.
So, to improve the quality of signals, repeaters are needed to be installed.
Functions of a Repeater
It receives an incoming signal from one device and retransmits it, forwarding it on to other.
There are two types of repeaters:
- Amplifier Repeaters It amplifies or boosts the incoming signals. So, it amplifies both the signal and any concurrent noise.
- Signal Repeaters These repeaters remove or filter the noise from incoming signals and retransmit the same, in the same way as it was starting from the source.
5. Gateway The gateway is a network device which is used to connect dissimilar networks. The gateway establishes an intelligent connection between a local network and external networks, which are completely different in structure.
Infact, the gateway is a node that routes the traffic from a workstation to outside network. The gateway also acts as a proxy server and a firewall, which prevents the unauthorised access.
Functions of a Gateway The gateway is a node in a network which serves as a proxy server and a firewall system. It is associated with a router and a switch. Its main function as proxy server is to hold the information from a website temporarily so that the repeated access to the same website or web page could be directed to the proxy server instead of actual web server, thus helps in reducing the traffic load. As a firewall system, it prevents the unauthorised access to and from a private network.
Network Protocols
Protocol refers to the set of rules and regulations applicable for a network. The protocol defines standardised format for the data packet to be transmitted through the network, techniques for detecting the errors whenever they arise and methods to correct these errors and so on.
Some of the commonly used protocols are as follows:
1. HTTP (HyperText Transfer Protocol) HTTP is an application level protocol and it is widely used for viewing information of a web page over Internet. It is a generic, stateless and object oriented protocol.
HTTP consists of a set of requests from the browser of a local computer to the web server and a set of responses going back to the other way.
Though HTTP is designed for the use in the web application but it has scope to be used in future object oriented applications.
2. FTP (File Transfer Protocol) FTP is designed to transfer files from one system to another. Using FTP, different people locating in different geographical locations can cooperate and work on a common project. FTP is designed to promote sharing of files and to encourage the indirect use of remote computers. Using FTP, any type of file can be transferred from one computer to another. Though for transferring files, we have to specify whether the file is in ASCII format or in binary format.
3. TCP/IP (Transmission Control Protocol/Internet Protocol) TCP/IP is a set of two protocols, i.e. TCP and IP. The Internet Protocol (IP) tells how packets of information are sent out over networks. IP has a packet addressing method that lets any computer on the Internet forward a packet to another computer that is a step closer to the packet’s recipient. The Transmission Control Protocol (TCP) ensures the reliability of data transmission across Internet connected networks. TCP checks packets for errors and submits requests for retransmission if errors are found.
4. PPP (Point-to-Point Protocol) The PPP is used with dial-up Internet connections including ISDN. It is a layered protocol, which is used for transmitting the data over usual telephone lines. It can provide connection authentication, transmission, encryption and compression.
Remote Access Software
In remote access software firstly we have to know about the term “remote access”. Remote access refers to the ability to access a computer or a network from a remote distance. Remote access can be established via a line that runs between a computer and Local Area Network. This type of line provide faster speeds but has the drawback of being more expensive. Another suitable method for performing remote access by establishing a Virtual Private Network, which is usually uses the Internet to connect remote site and users together.
To establish a remote connection, both the local machine and remote computer/server must have remote access software. Remote access software dial indirectly to the network server.
Team Viewer is one of the example of Remote Access Software. It simplifies remote access over the Internet and supports a wide range of devices. It is free for private uses.
Internet
The Internet has gained popularity and emerged as an important and efficient means of communication. The Internet is world wide network of networks.
Through Internet, computers become able to exchange information with each other and find diverse prespective on issue from a global audience.
Basic Components for the Working of Internet
Here, we are discussing some basic yet essential components of a network which are very much required for the proper functioning of the Internet.
IP Address
An IP address is an identifier for a computer or device on a TCP/IP network. It is a way to measure a user’s unique identity. The traditional IP Addresses (IPv4) uses a 32-bit numeric format and it defines both network and host address. But now-a-days a new version of the IP protocol (IPv6) has been invented to offer virtually limitless number of unique addresses. An IP address can be static or dynamic. A static IP address will never change and it is a permanent Internet address. A dynamic IP address is a temporary address that is assigned to any computing device to access the Internet. An example of IPv4 address is 216.3.128.12. Each number can be from zero to 255.
MAC Address (Media Access Control Address)
The MAC address refers to unique physical address assigned to a Network Interface Card (NIC). Every workstation or device which is connected with the network has unique node address. The MAC address is a 6 byte (48 bit) address. Each byte in this address is separated by a colon. There are hexadecimal numbers from 00 to FF (i.e. 0 – 255) in each byte, e.g. 05 : C2: 04 : 59 : 2F: BC is a MAC address.
Domain Name
Domain name is a unique name or identification that helps to create the path to open a particular website. All the domain names have IP addresses. IP address can be remembered by the computer, but it is difficult to remember for a human being. If you know that URL (Uniform Resource Locator) of a website, you can access it. The URL is actually the domain name of website, so the domain name is unique name of a website. Every time we enter a domain name it will be converted into an IP address and the website will be opened, e.g. www.Mybook.com A domain name contains three parts:
- Host name as, www
- Name describing the website purpose as, Mybook
- Top level domain as .com, .net, .edu, etc.
Domain Name Resolution
Domain name resolution refers to the process of getting the corresponding IP address from a domain name. Infact the content of a website is stored on some server anywhere in the world and to access the information or content the IP address is required. When we enter the domain name in a browser by typing on the address bar, the browser issues a command to the operating system to provide the corresponding IP address.
Thereafter, the operating system searches the host file in which IP address of some domains are stored. If the corresponding domain name was not found there, then request is forwarded to Domain Name Servers (DNS). The DNS maintains a directory of all domain names and corresponding IP addresses registered on the Internet. When the IP address is required, it is provided to the browser. The browser can access the information from the respective website using the IP address.
Internet Applications
Applications which runs by the use of Internet are given below:
1. E-Mail
E-mail stands for Electronic Mail. It is a text message that may contain files, images or other attachment sent through a network to a specified individual or group of individuals. Some early e-mail systems required that the sender and the recipient both be online at the same time, in common with instant messaging. Today’s e-mail systems are based on a store and forward model. E-mail servers accept, forward, deliver and store messages. Neither the user nor their computers are required to be online simultaneously; they need to connect an e-mail server, for as long as it takes to send or receive messages. Interaction between e-mail server and clients are governed by e-mail protocol. The two most common e-mail protocols are POP3 and SMTP.
2. SMS
SMS stands for Short Message Service. Short text messages are transmitted to and from a mobile phone, fax machine, etc. Message must not be longer than 160 alpha-numeric characters and may also contain images or graphics. Once a message is sent, it is received by a Short Message Service Centre (SMSC), which must get to the appropriate mobile device. To do this, the SMSC sends a SMS request to Home Location Register (HLR) to find the roaming customer. Once the HLR receives the request, it will respond to the SMSC with the subscriber’s status
- Inactive or active.
- Where subscriber is in roaming.
If the response is ‘inactive’, then the SMSC will hold on to the message for a period of time. When the subscriber access his device, the HLR sends a SMS notification to the SMSC and the SMSC will attempt delivery. The system pages the device and if it responds, the message gets delivered. The SMSC receives a verification, that the message was received by the end user, then it is categorised as, send message and will not attempt to send again.
3. Video Conferencing
By the name itself it is clear that it is the process of conferencing through video talk. Basically, video conferencing is a type of conference, which takes place between two or more participants by using computer networks to transmit audio and video data. For such type of video conferencing each participants should have a video camera, microphone and speakers in his computer set-up.
There are two types of video conferencing:
- Point to Point
- Multipoint.
1. Point to Point Video Conferencing is a conferencing between two person through video. It is like video telephonic call. The difference in a simple telephonic call and point to point video conferencing is the virtual appearance of user. They are able to view each other on their computer window screen.
2. Multipoint Video Conferencing allow more than two participants to sit in a virtual conference room can communicate with others as if they are sitting just next to each other.
4. Voice Mail
Voice mail is basically a voice message that stores messages electronically which can be retrieved by the intended recipients according to their convenience. Voice mail was developed by telephony to prevent missed calls and to facilitate call screening. Now-a-days, voice mails are getting integrated with Internet, which allows users to receive incoming voice message on their computers.
5. Chat
It can be defined as an informal conversation between two or more people. In terms of computers, chat refers to the communication between two users through computer, textually. The text is entered by one participant through keyboard and that text is received by other on the other side and vice versa.
Wireless/Mobile Communication
By the name itself, it can be defined that it is a communication which do not use any wires for the transmission of data. In this type of communication, waves are used as the transmission medium, instead of wires. Mobile communication uses electromagnetic waves for sharing and transferring of data. Some of the mobile communication such as GSM, CDMA, WLL, 3G and 4G are discussed below:
1. CDMA (Code Division Multiple Access)
CDMA stands for Code Division Multiple Access. It is a digital cellular technology that uses spread spectrum techniques. CDMA consistently provides better capacity for voice and data communications than other commercial mobile technologies, allowing more subscribers to connect at any given time and it is the common platform on which 3G technologies are built. CDMA is a military technology first used during world war II by english allies to foil german attempts at jamming transmission.
2. GSM (Global System for Mobile Communication)
GSM is developed to describe protocols for second generation (2G) digital cellular networks used by mobile phones. It is developed by the European Telecommunications Standards Institute (ETSI) for the replacement of first generation (1G) analog cellular networks and originally described a digital circuit switched network optimised for full duplex voice telephony. Full duplex means receives and sends the data at a time. ‘GSM’ is a trademark owned by the GSM Association.
3. WLL (Wireless Local Loop)
It is an ideal application which provides telephone service to a remote rural area. This technology simply means that the subscriber is connected to the nearest exchange through a radio link instead of through the copper wires. Sometimes it is also known as Radio In The Loop (RITL) or Fixed-Radio Access (FRA). WLL has an advantage over satellite broadband because of its lower transmission delay.
The system used in WLL is based on full-duplex radio network whose capacity is very high to access the data from network. The cost of installing a WLL system for subscriber access lines is now virtually the same as that of copper cable, though it can vary depending on the subscriber line length and local conditions, e.g. A PHS-WLL system has already been commercialised and is scheduled to be implemented for commercial service in several countries.
4. 3G (Third Generation)
3G stands for Third Generation and it is also called Tri-Band 3G. 3G telecommunication networks support services that provide an information transfer rate of atleast 200Kbps. This will allow 3G mobile devices to support services such as video footage conferencing and full Internet access. Recent 3G releases, often denoted 3.5G and 3.75G, also provide mobile broadband access of several Mbps to smart phones, modems, laptops, computers.
5. 4G (Fourth Generation)
4G stands for Fourth Generation, the stage of broadband mobile communications that will supersede the third generation (3G). Carriers that use Orthogonal Frequency Division Multiplexing (OFDM) instead of Time Division Multiple Access (TDMA) or Code Division Multiple Access (CDMA) are increasingly marketing their services as being 4G, even when their data speeds are not as fast as the International Telecommunication Union (ITU) specifies.
According to the ITU, a 4G network requires a compatible device to exchange data at the rate of 100 Mbps. A 3G network, on the other hand, can offer data speeds as slow as 3.84 Mbps. From the consumer’s point of view, 4G is more a marketing term than a technical specification but carriers feel justified in using the 4G label because it lets the consumer know that they can expect significantly faster data speed.
Network Security
Network security refers to the provisions and policies adopted by the network administrator to prevent and monitor unauthorised access, misuse, modification or denial of the computer network and network accessible resources. For network security, there is a provision of assigning an ID and a password or other authenticating information that allows the user to access the information and program within their authority. Network security covers a variety of networks; both public and private. Network security is important because people, organisations, corporates across the world are using Internet to store the data, for communicating and transmitting critical information. That is why network security breaches are there.
Some of the major network security breaches are:
1. Denial of Service (DOS)
A denial of service attack refers to an attempt to make computer resources unavailable to the intended users. Generally, it consists the effort of a person or a group of persons to prevent an Internet site or service from functioning efficiently or completely. It may be temporarily or infinitely. One of the common methods of denial of service attack is to saturate the target machine with external communication requests, in such a way that either the machine can not respond properly or respond slowly that is would not send services effectively.
2. Intrusion Problem
The intrusion problem refers to the malicious activities or policy violation performed on a computer system. The main motive of intrusion is to tress vital information and essential data. Such type of activities are performed by the people having malicious mentality.
- Intrusion Detection System It is a device or software application that monitors the network for the malicious activities. The intrusion detection and prevention system is primarily focused on identifying possible incidents, logging information and reporting attempts.
- Snooping It refers to unauthorised opening of files or accessing data, e-mail, etc. Snooping may include monitoring and tracing of keystrokes pressed, capturing the passwords and login information, etc.
- Eavesdropping It is identical to snooping. When there is intentional interception of other data such as e-mail, login-id, credit card information, password, etc., then it is said to be eavesdropping. In other words, when someone listens or intercepts others data secretly, then it is said to be eavesdropping.
3. Authentication
It provides a way of identify a user. It also known as the term of password protection. The user is provided with an legal login-id and password by which he/she is considered to be an authentic user and is allowed to see the password protected data.
Network Security Concepts
Network security refers to the security of the network resources which are used and guided by Internet as they are very much unwanted viruses and many other problems which can damage the active files over the network. Some of the network security concepts are described below:
1. Cookies
It is also known as browser cookies or tracking cookies. Cookies are small, often encrypted text files, located in browser directories. They are used by web developers to help users navigate their websites efficiently and perform certain functions. Due to their core role of enhancing enabling usability or site processes, disabling cookies may prevent users from using certain websites. Cookies are created when a user’s browser loads a particular website. The website sends information to the browser which then creates a text file. Computer cookies are created not just by the website the user is browsing, but also by other websites that run ads, widgets and other elements on the page being loaded. These cookies regulate how the ads appear or how the widgets and other elements function on the page.
2. Firewall
A system based on software or hardware designed to prevent unauthorised access to or from a private network. Firewalls may be combination of hardware and software. A firewall establishes a barrier between a trusted, secure internal network (private network) and another network that is not assumed to be secure and’ trusted. All messages entering or leaving the Intranet (internal network) pass through the firewall, which examines each message and blocks those that do not meet the specified security criteria.
There are several types of firewall techniques:
- Packet filter Looks at each packet entering or leaving the network and accepts or rejects it based on user defined rules. Packets filtering is fairly effective and transparent to users, but it is difficult to configure. In addition, it is susceptible to IP spoofing.
- Application gateway Applies security mechanism to specific applications, such as FTP and Telnet servers. This is very effective, but can impose a performance degradation.
- Circuit-level gateway Applies security mechanism when a TCP or UDP connection is established. Once the connection has been made, packets can flow between the hosts without further checking.
- Proxy server Intercepts all messages entering and leaving the network. The proxy server effectively hides the true network addresses.
3. Cyber Law
Cyber law is a term that encapsulates legal issues related to the use of Internet. It is less a distinct field of law than intellectual property or contract law, as it is a domain covering many areas of rules and regulations. Some leading topics include Internet access and usage, privacy, freedom of expression and jurisdiction.
4. Hacker
A hacker is someone who seeks and exploits weaknesses in a computer system or computer network. Hacking is the practices of modifying the features of a system, in order to accomplish a goal outside of the creator’s original purpose. Hackers obtain advanced knowledge of operating systems and programming languages. Hackers are most commonly associated with malicious programming attacks on the Internet and other networks.
5. Cracker
A cracker is also called black hat hacker. A cracker is an individual with extensive computer knowledge whose purpose is to breach or bypass Internet security or gain access to the software without paying royalties. The general view is that, while hackers build things, crackers break things. Cracker is the name given to hackers who break into computers for criminal gain. Crackers’ motivations can range from profit, a cause they believe in, general maliciousness or just because they like the challenge. They may steal credit card numbers, leave viruses, destroy files, etc.
6. Trojan
A Trojan, or Trojan Horse, is a non-self-replicating type of malware which appears to performs a desirable function but instead facilitates unauthorised access to the user’s computer system. Trojans do not attempt to inject themselves into other files like a computer virus. It may steal information, or harm their host computer systems. Trojans may use drive-by downloads or install via online games or Internet-driven applications in order to reach target computers. Unlike viruses, Trojan horses, do not replicate themselves.
e.g. Beast, Sub7.Zeus, Zero Access Rootkit, etc.
We hope the given CBSE Class 12 Informatics Practices Notes Chapter 1 Computer Networking Pdf free download will help you. If you have any query regarding NCERT Class 12 Informatics Practices Notes Chapter 1 Computer Networking, drop a comment below and we will get back to you at the earliest.